30 Cybersecurity FAQ - How To Protect Your Business
30 Cybersecurity frequently asked questions answered for you.
Insider Cybersecurity Secrets of How to Protect Your Business.
Cybersecurity Questions - Click question to link to answer.

Do companies need cybersecurity?
How can I protect my business from cyber attacks?
How can companies prevent security breaches?
How do I get started with Cybersecurity?
How do I stop credit card fraud?
How has cyber security changed in the last decade?
How is cyber risk calculated?
How much does a cyber security consultant make?
Is now a good time to start a career in cyber security?
Is real-time attack detection the future of cyber security?
What are the best cyber security courses?
What are the best cyber security resources?
What are the career options in cybersecurity?
What are the five phases of the NIST cybersecurity framework?
What are the objectives of Cyber Security?
What are the uses of AI in cyber defence?
What is a cyber risk assessment?
What is a security risk assessment?
What is an information security framework?
What is an IT vulnerability assessment?
What is computer security?
What is cyber threat analysis?
What is cybersecurity?
What is information security governance?
What is the best defense against social engineering?
What is the biggest cyber security threat to your business?
What is the cyber security strategy?
What is the future of cyber security?
What is threat intelligence in Information security?
Why is cyber security really a business problem?
Cybersecurity Introduction
The internet is a dangerous place.
With cybercriminals and hackers, there's always the fear of your personal information being compromised.
But how much do you really know about cybersecurity?
If you're looking to take precautions against identity theft and other online threats, here are some answers to common questions about cybersecurity:
Cybersecurity Questions and Answers
Do companies need cybersecurity?
Every company and every person has sensitive data that needs protection, and it's never too soon to start protecting your business or personal information from thieves and criminals. Cybersecurity is all about preventing unauthorized access to, use of, disclosure of or damage to an organization's assets (in this case, data) by malicious activity such as hacking. Cyber security includes activities such as firewalling (using software designed for this purpose), installing anti-malware updates if the system detects a threat on a device with malware attached, identity theft protection services which protect against identity theft in case a network is hacked into and then personal information compromised, encryption software that scrambles digital data so that it can't be read by anyone who did not encrypt it, cyber security insurance in case a cyber-attack causes damage to the business and cyber extortion which is when criminals demand money in return for not releasing data that they have hacked into.
How can I protect my business from cyber attacks?
Broadly, there are four types of cyber attacks that may compromise your business's sensitive data—electronic communication interception, computer network exploitation, Denial-of-Service attacks to networks and computers, and physical access. The first step in protecting the integrity of your businesses sensitive information is understanding which type of attack can be made to it—those listed above are what I would consider the most common. Once done you'll have a better idea about how to protect yourself from any one threat. Lastly examine your own internal practices as part of this process as well such as training on new technologies and social media security policies for employees. What you end up doing is up to you but this list should help you know where to start!
How can companies prevent security breaches?
Managing personal information is crucial to any company's security. Cyber criminals are experts at collecting data on potential victims to steal valuable information, so it is important for companies to keep their system safe by ensuring that they have installed an up-to-date antivirus software and firewall. They also need to take care not store sensitive users data in the cloud without having a way of protecting it; this can come in the form of encryption or limited rights access. Additionally, organizations should employ a security team who will be outfitted with the proper knowledge and training on how to protect against these breaches like social engineering attacks (phishing) or spear phishing (targeted e-mails). Finally, make sure your employees are educated about these issues; no security team will be able to protect your personal information as well as a vigilant and informed user.
How do I get started with Cybersecurity?
Advancing your career into the cyber security domain is a good first step. There are three main avenues of distinction, which consist of security professionals, penetration testing and threats management. Learning about all three skill sets will help you determine which one fits more adequately for you and will ultimately lead to feeling competent and confident in your abilities.
How do I stop credit card fraud?
Effective measures to stop credit card fraud are to protect your credit card number, compare costs and benefits of shopping online, report lost or stolen cards immediately, keep an eye on your account statements for un-authorized purchases.
How has cyber security changed in the last decade?
Cyber security has changed in many ways over the years, with emphasis on more vulnerabilities in newer technologies, how data is stored and accessed, hacking skills that are available to everyone, nation state intelligence operations for cyber intelligence, large scale distributed denial of service (DDoS) attacks for political purposes. Mobile devices have given rise to the BYOD trend - Bring Your Own Device. However this means increased risk associated with having access to your email or company database through mobile devices if not properly secured. Businesses are finding new threats every few months which are difficult to keep up with due to their rapid evolution. Nation states around the world are being equipped with cyber warfare capabilities that were once only reserve for the most advanced countries just a decade ago.
How is cyber risk calculated?
Cyber risk is calculated by determining the likelihood or improbability of a cyber-attack (measured in percentage of likelihood) and the organization’s budget (our monetary defence). Organizations that have greater risks are then advised to increase their security focus accordingly. It is also important to create a detailed list of protocols, control systems, etc., before any assessment can be conducted. Risk assessments are completed in accordance with industry standards for evaluating enterprise risk. The goal of these assessments is to minimize the impact on an organization's mission accomplishment in the face of operational disruption due to an event with significant probability or consequence levels. Risk management aims at ensuring that the assessed risk will not cause more damage than it would cost for mitigating them beforehand.
How much does a cyber security consultant make?
The starting annual salary for a cyber security consultant is about $90,000. This includes income from the consultant's employer, consulting fees and any benefits they receive. Internally, many companies maintain an entire department of security engineers that may specialize in one or more areas like network monitoring, intrusion detection or forensics analysis. Consulting firms may offer services ranging from designing proper business networks to providing training on how to avoid attracting hackers.
Is now a good time to start a career in cyber security?
If you want to get a job in the cybersecurity field, now is a perfect time to start. Cybersecurity careers are proliferating and expanding rapidly while demand remains high. Numerous higher education avenues exist for adults that want to change occupation or enter a new one which furthers them in their career goals through needed certification programs, degree programs, and continuing education opportunities. Furthermore, there's never been greater need than right now for cybersecurity professionals due to the massive shift toward an internet-connected world where everything frequently seems under attack by some malicious entity. All signs point to one thing: cyber security jobs are here for the long haul with security experts ultimately able to benefit greatly from it professionally.
Is real-time attack detection the future of cyber security?
Yes. Today, cyber attacks are coming in at an unprecedented rate, but that's just the tip of the iceberg when it comes to new attack vectors that will only increase in number and intensity moving forward. Given current business realities, incidents can quickly lead to loss of revenue and trust on company brands. Thus proactive security strategies based on three areas - threat landscape, threat detection by humans or AI, and incident response - offer companies best protection against modern-day data breaches. However, despite unreal advances made in technology over the last 20 years businesses continue to fail spectacularly when it comes for managing risk of hacking attempts. This is where artificial intelligence (AI) intervention is most needed; pairing AI with automation has proven highly successful whenever deployed.
What are the best cyber security courses?
Training courses, network security, cyber security certifications, and systems administration training programs are the best ways to learn about protecting a computer system from outside attack.
Cyber Security training is a must as hackers are constantly finding new ways to break into networks, systems and data. In fact, the threat is so real that it's not a question of if your system will be hacked, but when it will happen.
What are the best cyber security resources?
Department of Homeland Security - USA.gov
AusCERT - "Australian Computer Emergency Response Team (AusCERT) is the Australian Government's computer emergency response team."
NIST cybersecurity framework - The National Institute of Standards and Technology (NIST) has created this "Framework to manage risks in cyberspace so that people, businesses, and governments can have greater confidence in their networks and online transactions" for private citizens.
What are the career options in cybersecurity?
Generally, there are two categories of career options in cybersecurity: (1) cybersecurity specialists and (2) security management professionals.
Security specialist jobs include: information assurance analysts, network engineers, security systems administrators and programmers.
Security management professionals include: chief information officers, legal advisors/lawyers who specialize in cyber law, chief communications and strategy officers. The majority of these careers need associate's degree or some post-secondary education like a bachelor's degree before you get started at the entry-level - that is to say entry-level not just for your current job but for industry as a whole.
What are the five phases of the NIST cybersecurity framework?
The five phases of the NIST cybersecurity framework are:
-Assets: Tracks which assets on a network or on an internet site have been designated as important, and who has access to them. This process helps administrators establish who is authorized to perform what role in a business's security environment, while also limiting the number of people given unnecessary administrative privileges.
-Protect: Ensures that all industry regulations and best practices are implemented across a company's entire product line. Protect includes processes such as patch management, vendor risk management, capabilities development life cycle management for software engineering projects, release control management for software engineering projects, configuration control for information systems engineering projects, IT asset disposal due diligence process audit compliance program design and implementation.
-Detection: Detects, analyses and responds to indicators of compromise in an organization's assets. This process helps administrators establish how frequently they want to be notified about certain events occurring on a network, such as sending out patches from vendors or from the organization itself.
-Recovery: Ensures that after assets have been compromised, only trustworthy assets are allowed on the network, assets which have been verified to meet standards. This process then restores compromised assets to their original state or finds replacements for them that can be trusted
-Continual Improvement: Helps ensure that the organization makes changes in response to lessons learned throughout all of the other phases of the framework, and also ensures that the process itself is continually improving.
What are the objectives of Cyber Security?
Cyber Security's primary objective is to protect information and other digital assets against network security threats, cyber-attacks, system failures, natural disasters, malicious software (malware), theft of data or any unauthorized access.
What are the uses of AI in cyber defence?
Artificial intelligence (AI) aids cyber defence in a number of ways. One way is to apply AI tools to security purposes, such as analysing for signatures or irregularities in the data stream. AI also helps provide an advanced level of threat detection by scanning networks, detecting patterns and identifying abnormal activity. There are many other uses for artificial intelligence which will increase efficiency and reduce human error in the cyber security industry, while having large benefits on both individuals and businesses alike.
What is a cyber risk assessment?
A cyber risk assessment is the process of identifying all possible vulnerabilities and creating controls to prevent them. The goal of a cyber security assessment is to identify weaknesses that an attacker could exploit, then determine how the organization could protect against those vulnerabilities. A cyber security plan should include both long-term security measures as well as incident response capabilities according to each institution's risk tolerance. Some key points to consider when putting together a High-Level Cyber Security Plan are: organizational roles and responsibilities for managing risks; enterprise architecture & frameworks considerations; application inventory, access controls & segmentation; mobile device management including mobile applications; network monitoring/filtration/logging - awareness intrusion alerts system (IDS), log aggregation, data retention policies within customized risk management risk tolerance. The risk assessment process is made up of four steps: risk identification, risk analysis, risk evaluation and risk response planning.
What is a security risk assessment?
A security risk assessment is a process for identifying and managing the risks associated with information systems. The objective is to identify assets, their value to business, estimate the value of loss from a compromise, put in place preventive controls for mitigating identified threats and damages from attacks that have already been detected. This is achieved by a series of formalized methods undertaken by qualified personnel during a process that includes probability analysis and cost benefit analysis. ISO 27001 sets out the requirements for frameworks within which an organization can do security risk assessments as well as other things such as gathering data about threats so the organization may decide how best to deal with them.
What is an information security framework?
An information security framework is essentially an operating model that defines your organization's governance, controls, and technical considerations for protecting critical data. There are three primary frameworks in the industry today including ISO 27001, the NIST Cybersecurity Framework (NTF), and Payment Card Industry Data Security Standards (PCI DSS). Each of these frameworks provides a standard set of prescriptive requirements to help organizations manage cybersecurity risks. By following all appropriate measures within one or more of these frameworks, organizations can reduce their risk profile to an acceptable level.
What is an IT vulnerability assessment?
A vulnerability assessment is an ongoing process that involves identifying vulnerabilities within your IT infrastructure and determining what needs to be done to reduce the risk of those vulnerabilities. This process covers a wide range of security-related concerns, including physical security, identity management, software and hardware updates, social engineering prevention procedures, etc. There are a variety of tools available for conducting vulnerability assessments from everything from manually analysing systems to using automated analysis. Some form greater coverage than others do as well as varying degrees in terms of comprehensiveness.
What is computer security?
Security is a process of identifying, preventing and/or mitigating potential risks to your system. The internet has obviously filled the space in which these risks exist. Two main aspects to security are confidentiality-ensuring that information is shared with only those who are authorised, and integrity-ensuring that the message content has not been tampered with in any way. Protection of computer systems can be achieved by applying appropriate controls to users, processes and technological devices for protection against unauthorised use or abuse.
What is cyber threat analysis?
Cyber threat analysis is the practice of evaluating risks and vulnerabilities to determine how best to protect against cyber attacks. It relies on input from multiple disciplines, including cyber security, information technology, risk management, economics etc., all to make sure that every part of the organization is secure. Basically, it's about knowing what types of threats can occur in your environment now or in the future so you can plan for them appropriately. Penetration testing is a tool used widely by organizations around the world during threat analysis because it acts as a real-time simulation of what would happen if an attack was executed on your system by telling you exactly where your weaknesses are before they are exploited for maximum gain.
What is cybersecurity?
Broadly speaking, cyber security means protecting against unauthorized access and malicious acts that breach an organization's virtual defense. The different types of security include network security, with technologies such as firewalls and anti-spam software; data security with the use of encryption to protect data from unauthorized access; and critical infrastructure protection with system hardening, intrusion detection systems, and intrusion prevention systems. Cyber attacks come in many forms, including intellectual property theft or vulnerability exploits for which a patch may be available but not deployed on all platforms.
What is information security governance?
Information security governance, aka governance is a collection of ongoing decisions, activities and initiatives to protect or manage an organization's information assets. When it comes to its use in the business world, information security governance is all about risk management through processes like conducting computer security audits, maintaining required data protection procedures and following industry best practices. Risks are assessed for each enterprise depending on factors such as volume of sensitive information handled, value of intellectual property created and maintained by the company along with the potential consequences if that data were compromised or became corrupted.
What is the best defense against social engineering?
Phishing attacks are becoming more commonplace, often impersonating an organization's website to harvest sensitive information. Employees should be trained in security awareness and receive regular computer based training. Software firewalls are also very important as they will help the manager to identify any unauthorized accesses or attempted hacking that may occur into the computer system. Once identified, it is recommended to contact technical support immediately about the intrusion attempt. Some settings can be changed on software firewalls that may block suspicious traffic from intruding, thereby preventing a potential intrusion before harm can come to company data or systems.
What is the biggest cyber security threat to your business?
A ransomware attack is one of the most dangerous cyber security threats. A hacker will lock or encrypt your data so fiercely that not even the owner can open it, unless they provide payment in some form for a key to unlock it. It's hard to estimate how much information has been lost due to these attacks because you don't know if someone paid for their lost information with bitcoin or other currency that isn't accounted on paper trails or currency exchanges sites like Bloomberg. The second most dangerous, but equally common threat facing businesses today are phishing emails which are designed by scammers who want to steal your valuable data such as credit card numbers and account login credentials.
What is the cyber security strategy?
A cyber security strategy is about recognizing current threats, being aware of risks or vulnerabilities based on the harm to the organization or system, assessing the impact to safety and property, protecting against liabilities through proactive measures, preventative actions and responses. It's about protecting intellectual property through authentication capabilities that are self-service. Implementing boundary protection by including an organization's IT network via firewalls that separates networks into public areas which are open to attacks from outside networks and private areas with restricted access where only staff members have permission. This separation provides a level of protection since one area cannot be seen nor attacked by another area. Generating alerts during login attempts can trigger staff to monitor for suspicious activity which may lead them towards discovering insider threats as well as preventing an outside threat from accessing resources. A cyber security strategy provides proper documentation and training with staff to protect against liability issues such as negligence, lack of due diligence and foresight or not meeting regulatory compliance requirements that can lead to fines or penalties.
What is the future of cyber security?
Cybersecurity is changing rapidly. Along with this, new terms are being introduced which will be new to most general audiences. Computers and smartphones can be hacked remotely without ever having touched them physically through unsecured networks or the Internet of Things (IoT). Ubiquitous connectivity has led to increased automation, but machine learning algorithms have been proven vulnerable in several high-profile events. As a result, organizations have sought remote working arrangements where employees can work securely from anywhere in the world where there's an internet connection.
What is threat intelligence in Information security?
The term cyber threat intelligence is a new one in the cybersecurity field, but it has already permeated organizations and become an influential part of how they handle security. Threat landscape refers to the risks, threats, vulnerabilities and likely events that could happen under certain conditions. These can be either external opportunities for attack or risks from internal failures . In other words, I'm not just thinking about how to protect my own laptop from being hacked, but also about what hackers might be trying to do next against this firm. Expertise in understanding these changes in the risk environment is another important element of cyber threat intelligence companies offer companies a way of prioritizing protections and investments by estimating their likelihood and potential severity.
Why is cyber security really a business problem?
Detection of cyber breaches is becoming more difficult, costly, and time-consuming. Attacks are more sophisticated and they keep evolving. Not only do these trends increase the risk, but also cyber intruders are consistently getting smarter in their methods. A data breach is inevitable when you operate in a digital world with so many people who can remotely access any data intended for consumption via the internet. Furthermore, it doesn't take much to compromise sensitive enterprise data that carries value or privileged information. Once detected, organizations face different challenges when addressing security threats--these range from how to detect threats to how best to prevent them from taking root in your network infrastructure in the first place.
Cybersecurity Conclusion
In light of the recent slew of data breaches and cyberattacks, it's more important than ever to take cybersecurity seriously.
Data security is a crucial element in today’s digital world.
You can protect your personal information by being vigilant about what you share online and using secure passwords that are difficult for hackers to guess or crack.
But there's one thing many people don't think about when discussing cybersecurity - the need for a robust backup plan!
If your business data gets corrupted or destroyed, how will you be able to recover?
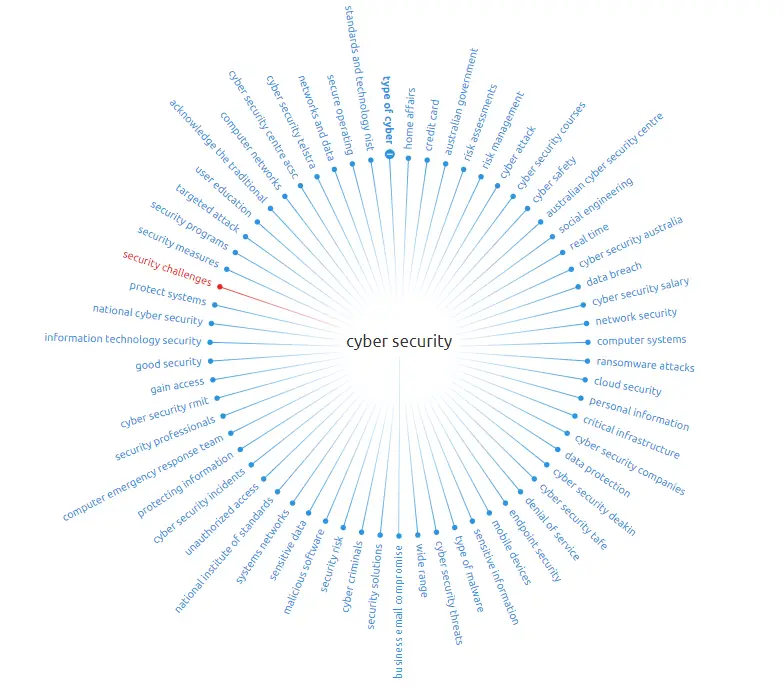
Cybersecurity Mindmap